Control What Your
Internal Systems
Cannot See
AlphaVecta helps financial institutions uncover hidden structural exposure within control environments.
Most financial institutions maintain sophisticated monitoring systems, audit frameworks, and compliance programs. Yet internal fraud losses and control failures continue to emerge across the global banking sector.
This is because traditional systems measure transactions and reported incidents. They rarely measure behavioural drift, process bypass patterns, privilege inflation, and structural weaknesses that develop inside operational environments over time.
Core Advisory Capabilities
We assess the behavioural and operational conditions that create exposure inside institutional control environments. Using structured risk modeling and exposure diagnostics, we identify areas where policy deviation, privilege inflation, and operational workarounds create structural vulnerability.
Behavioural Drift Detection
Identify deviations between defined policy procedures and actual operational behaviour
Privilege & Access Analysis
Detect role inflation, dormant access privileges, override patterns, and anomalies
A structured diagnostic engagement designed to quantify institutional exposure within a defined timeframe. The engagement includes controlled data intake, behavioural risk modeling, and an executive exposure intelligence report delivered to senior leadership.
Behavioural Deviation
Access & Privilege
Process Integrity
Cultural Incentive Risk
Process Exception
30
Privilege Irregularities
6
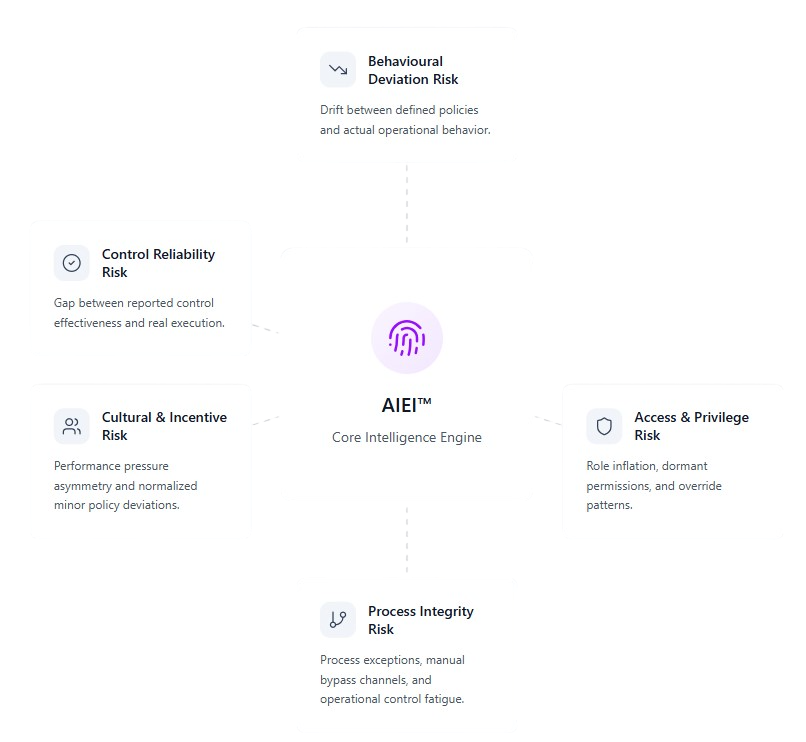
The AlphaVecta Institutional Exposure Index (AIEI™).
AIEI™ is a structured diagnostic model that quantifies internal fraud exposure across five behavioral risk dimensions
AIEI™ Core Intelligence Engine
AIEI™ quantifies internal fraud exposure across five institutional dimensions:
Governance
Safeguards
AlphaVecta engagements follow strict governance protocols including anonymized data ingestion, non-interference with production systems, and executive-only reporting.
Our work complements existing audit, compliance, and regulatory frameworks rather than replacing them.
Key safeguards include:
• Tokenized data ingestion
• No production system disruption
• Confidential executive reporting
• Clear separation from operational decision layers